Threat Actors Violating Computer Security: Understanding the Landscape
Threat actors violating computer security for personal gain have become a prevalent concern in today’s digital landscape. These malicious entities, driven by various motivations, employ sophisticated techniques to compromise computer systems, steal sensitive information, or disrupt operations. Understanding the landscape of threat actors, their methodologies, and the impacts of their actions is crucial in developing robust cybersecurity strategies. In this article, we delve deeper into this topic to provide insights and actionable recommendations for safeguarding against cyber threats.
Introduction to Threat Actors
Threat actors encompass a diverse range of individuals or groups with malicious intent towards computer systems and networks. They may include hackers, cybercriminals, nation-states, and insiders. Each category of threat actor possesses unique characteristics and motivations.
Defining Threat Actors
Threat actors are individuals or groups who exploit vulnerabilities in computer systems to gain unauthorized access, steal data, or disrupt operations. Their actions can have significant consequences for individuals, organizations, and even national security.
Motivations Behind Their Actions
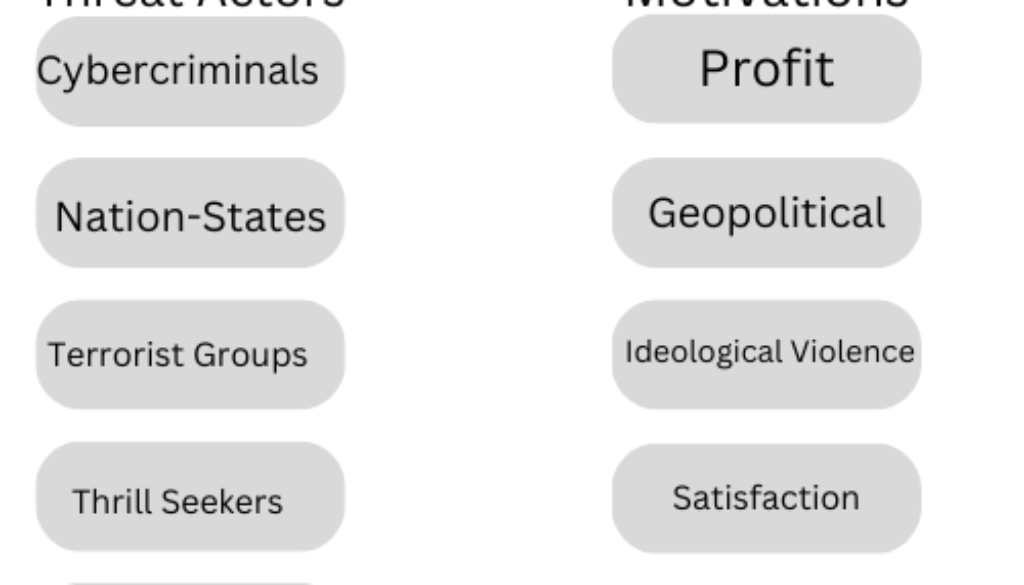
Understanding the motivations driving threat actors is crucial for anticipating and effectively mitigating potential cyber threats. Threat actors may be motivated by various factors, including:
Financial Gain
One of the primary motivations for threat actors is financial gain. Cybercriminals often target individuals, businesses, or organizations with the aim of extorting money or stealing valuable financial information. These actors may engage in activities such as ransomware attacks, identity theft, or credit card fraud to achieve their monetary objectives. The lure of quick and substantial profits incentivizes cybercriminals to continuously refine their tactics and exploit vulnerabilities in computer systems.
Political Ideology
Some threat actors are driven by political ideology and seek to advance their agenda through cyber attacks. Hacktivist groups, for example, may target government agencies, corporations, or institutions that they perceive as oppressive or unjust. These actors aim to raise awareness, promote political change, or disrupt operations in support of their cause. The anonymity and global reach of the internet provide a platform for hacktivists to amplify their message and garner attention for their grievances.
Personal Vendettas
In certain cases, threat actors may be motivated by personal vendettas or grievances against specific individuals or organizations. These actors may seek revenge, retaliation, or simply derive satisfaction from causing harm to their targets. Personal vendettas can manifest in various forms of cyber attacks, ranging from targeted harassment to deliberate sabotage of systems or networks. The emotional investment and determination of threat actors with personal vendettas make them particularly persistent and difficult to deter.
Thrill or Challenge
For some threat actors, the thrill of outsmarting security measures or the challenge of breaching high-profile targets is a motivating factor. These actors may engage in cyber attacks not necessarily for financial gain or ideological reasons but for the sheer excitement or prestige associated with their exploits. Such individuals may view hacking as a form of intellectual pursuit or competitive sport, seeking recognition within underground hacker communities or online forums. The adrenaline rush of successfully penetrating a secure system fuels their continued engagement in cybercriminal activities.
Espionage and Intelligence Gathering
Nation-states and state-sponsored threat actors may engage in cyber espionage to gather intelligence, monitor adversaries, or gain strategic advantages. These actors may target government agencies, military institutions, or critical infrastructure with the aim of acquiring sensitive information or disrupting operations. The information obtained through cyber espionage can be used for political, military, or economic purposes, shaping international relations and influencing geopolitical dynamics.
Psychological or Societal Factors
Psychological or societal factors may also play a role in motivating threat actors to violate computer security. Some individuals may feel marginalized, disenfranchised, or alienated from mainstream society, leading them to seek validation or empowerment through cyber attacks. Additionally, societal norms or cultural influences may contribute to the normalization of cybercrime in certain communities, perpetuating a cycle of criminal behavior.
Understanding the diverse motivations driving threat actors is essential for developing effective countermeasures and mitigating the risks posed by cyber threats. By addressing underlying grievances, improving cybersecurity defenses, and fostering cooperation between stakeholders, organizations can better protect against malicious activities and safeguard digital assets.
Types of Threat Actors
Hacktivists
Hacktivists are individuals or groups who use hacking techniques to promote political or social causes. They often target government agencies, corporations, or other organizations they perceive as oppressive or unjust.
Cybercriminals
Cybercriminals operate with the primary goal of financial gain. They may engage in activities such as identity theft, credit card fraud, or ransomware attacks to extort money from their victims.
Nation-States
Nation-states leverage cyber warfare tactics to achieve strategic objectives, such as espionage, sabotage, or political influence. These actors often have significant resources and advanced capabilities at their disposal.
Insiders
Insiders pose a unique threat as they already have authorized access to systems and networks. These individuals may abuse their privileges for personal gain or inadvertently compromise security through negligence or error.
Methods Employed by Threat Actors
Malware Attacks
Malware, including viruses, worms, and trojans, is a common tool used by threat actors to infiltrate and compromise computer systems. These malicious programs can steal sensitive information, disrupt operations, or provide unauthorized access to attackers.
Phishing
Phishing attacks involve the use of deceptive emails, websites, or messages to trick users into revealing personal information or clicking on malicious links. These attacks often target individuals or organizations with the aim of stealing login credentials or sensitive data.
Denial of Service (DoS) Attacks
DoS attacks aim to disrupt the availability of a targeted system or network by overwhelming it with a high volume of traffic or requests. These attacks can render services inaccessible to legitimate users, causing financial losses and reputational damage.
Insider Threats
Insider threats involve individuals within an organization who misuse their access privileges to intentionally or unintentionally harm the organization’s security. These threats can be difficult to detect and mitigate, as insiders may have legitimate reasons for accessing sensitive data or systems.
Impacts of Computer Security Violations
Financial Losses
Security breaches can result in significant financial losses for organizations, including direct costs such as remediation efforts, legal fees, and regulatory fines, as well as indirect costs such as loss of customers and market reputation.
Reputational Damage
Security breaches can tarnish an organization’s reputation and erode customer trust. This can have long-lasting consequences, affecting future business opportunities and brand loyalty.
Legal Consequences
Organizations may face legal repercussions following a security breach, including lawsuits from affected parties, regulatory penalties for non-compliance with data protection laws, and damage to intellectual property rights.
National Security Risks
Cybersecurity breaches can pose significant risks to national security, including the theft of sensitive government information, disruption of critical infrastructure, or interference in democratic processes.

Case Studies
Notable Incidents of Security Breaches
- The Equifax data breach: In 2017, hackers gained access to the personal information of over 147 million individuals, including names, Social Security numbers, and credit card details.
- The WannaCry ransomware attack: In 2017, the WannaCry ransomware infected hundreds of thousands of computers worldwide, causing widespread disruption to businesses and organizations.
Lessons Learned
These incidents highlight the importance of proactive cybersecurity measures, including regular software updates, employee training, and incident response planning.
Read about: Manually Updating Your Display Driver in Windows 10
Strategies for Mitigation
Strengthening Cybersecurity Measures
Organizations should implement robust cybersecurity protocols, including encryption, multi-factor authentication, and network segmentation, to prevent unauthorized access and protect sensitive data.
Educating Employees and Users
Training programs and awareness campaigns can help employees and users recognize and respond to potential cyber threats, such as phishing emails or suspicious website links.
Collaboration with Law Enforcement Agencies
Cooperation between organizations and law enforcement agencies is essential in investigating cybercrime incidents, apprehending threat actors, and prosecuting offenders.
The Future of Cybersecurity
Emerging Threats
As technology continues to evolve, new cyber threats are likely to emerge, including attacks targeting Internet of Things (IoT) devices, artificial intelligence (AI) vulnerabilities, and quantum computing risks.
Technological Advancements
Advancements in cybersecurity technologies, such as machine learning algorithms, threat intelligence platforms, and blockchain-based solutions, will play a crucial role in defending against future cyber threats.
Conclusion
In conclusion, threat actors violating computer security pose a significant risk to individuals, organizations, and even national security. By understanding the motivations and methods of these actors, implementing proactive cybersecurity measures, and fostering collaboration between stakeholders, we can better defend against cyber threats and safeguard our digital assets.
Reference Links
- What Is Computer Security? (And Why It’s Important)
- Computer security | Definition & Facts
- Computer security